Bridging the Gap: How Interoperability Can Advance Health Equity
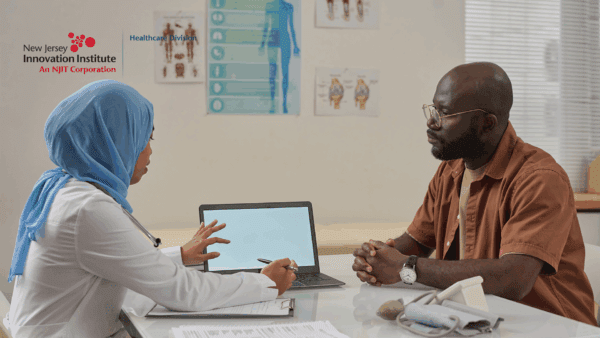
In healthcare today, achieving health equity remains a paramount challenge. Health equity means that everyone has a fair chance to be as healthy as possible, regardless of their socio-economic status, race, or geographic location. One promising way to achieve this goal is through interoperability—the …
Read more